Iris Recognition Market Size, Share, Outlook, and Opportunity Analysis, 2022 - 2030
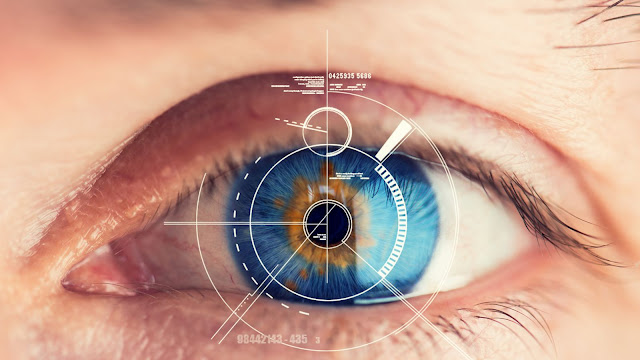
Iris recognition is essentially a
computerised biometric identification system that recognises mathematical
patterns on video images of one or both of an individual's eye irises. Eyes
have complex, novel, stable, and somewhat distantly visible patterns. This is
combined with video camera technology and subtly lit near-infrared illumination
for iris recognition in order to capture precise images of the intricate and
detailed structures of the iris that are visible from the outside. Blind people
can use Iris Recognition as long as they have an iris because it works with
contact lenses and regular glasses.
Over the course of the forecast
period, the iris
recognition market will likely experience significant growth in North
America. This is attributed to the increase in data breaches in the area, which
led to the adoption of biometrics in many industries to provide users with an
additional layer of security. Government agencies in the regions are also
putting iris scanning technology into use, which is fostering regional market
expansion. For instance, the National Crime Information Center and Next
Generation Identification (NGI) systems were developed jointly by the Federal
Bureau of Investigation (FBI) and state, local, federal, and tribal agencies
(NCIC).
The growing use of the iris
recognition system by both private and public organisations as a result of
growing security concerns is the main factor driving the global
iris recognition market. Iris can be seen from the outside, so scanning
is possible at a specific distance. Iris recognition can be used widely and is
easier to manage than a retina scan. These are a few of the elements promoting
the expansion of the world market. An additional factor that is anticipated to
spur the target market's growth is the increasing use of e-passports.
Additionally, because this technology is more precise and error-free, it is
considered to be more secure. The iris' patterns are distinctive and stable, so
there aren't any signs of error, making it a secure security method.



Comments
Post a Comment